Runtime governance for AI agents.
Set the rules for AI agents.
Decide before the agent acts.
Edictum checks agent actions before tools execute: allow, block, ask for approval, and record the decision across Python, TypeScript, and Go.
pip install edictum[yaml]pnpm add @edictum/corego get github.com/edictum-ai/edictum-goFeature taxonomy
Runtime governance is a set of concrete operating controls.
Runtime decisions
NowShould this agent action run right now?
Rulesets
NowWhat is this agent allowed to read, write, call, or return?
Workflow Gates
NowDid the agent follow the required process before moving on?
Approvals
NowWhich actions need a human decision before execution?
Audit evidence
NowCan we prove what happened later?
Replay / blast-radius
NextWhat would this rule change have changed?
SDKs and adapters
NowCan I use this with my current agent stack?
Gate CLI
NowCan Edictum control coding agents and local tool runners?
Reference stack
NowHow do teams coordinate visibility, approvals, and audit?
Security starters
NextWhat common agent risks can I cover immediately?
Workflow Gates
Enforce the process, not just the next call.
Workflow Gates are one feature family in the Edictum taxonomy: runtime rules control individual tool calls, while gates enforce ordered process across the run. An agent cannot skip from analysis to shipping unless Edictum has runtime evidence for each required stage.
Read / analyze
Spec, ticket, and relevant files were read
Implement
Writes stay inside the approved workspace
Verify
Tests, diff review, and scans completed
Review / approval
Human approval or required review recorded
Ship
Release tools open only after prior evidence exists
Stage progression depends on file reads, command executions, test results, approval decisions, and recorded stage state. If the evidence is missing, the next tool call is blocked or held for approval before it runs.
See Workflow Gates in the feature mapOperational agent profiles
Turn documented agent profiles into runtime rules.
Your architecture docs can classify the agent. Edictum makes that classification enforceable.
Edictum is strongest where agents touch real systems: scoped writes, ordered evidence, and human approval before business impact.
Read-only profile
Read-only
Inspect approved sources, summarize findings, and produce no side effects.
Scoped write profile
Scoped write
Make bounded changes, run verification, and pause for review before impact.
High-impact profile
Read/write + approval
Operate production tools only through evidence-backed stages and approvals.
Edictum measures behavioral conformance to a declared profile. It does not replace output-quality evals for accuracy, relevance, coherence, or answer quality. It composes with those evals.
Get started
See your first blocked call in 60 seconds.
Start with Runtime Decisions and Rulesets: the .env file was never read, the local decision ran before execution, and the decision log recorded everything.
1. The block
result = guard.evaluate("read_file", {"path": ".env"})
print(result.decision) # → block
print(result.block_reasons[0]) # → "Sensitive file '.env' blocked." 2. Three lines of code
from edictum import Edictum
guard = Edictum.from_template("file-agent")
# Done. Full enforcement.import { Edictum } from "@edictum/core"
const guard = Edictum.fromYaml("rules.yaml")
// Done. Full enforcement.import "github.com/edictum-ai/edictum-go/guard"
g, _ := guard.FromYAML("rules.yaml")
// Done. Full enforcement.3. Install
pip install edictum[yaml]pnpm add @edictum/corego get github.com/edictum-ai/edictum-gofile-agent
Block sensitive file reads and destructive bash commands
3 rulesresearch-agent
Session limits and PII detection for research workflows
3 rulesdevops-agent
Production deploy gates, ticket requirements, role checks
6 rulesnanobot-agent
HITL approvals for shell exec, sub-agent spawning, MCP tools
5 rulesFramework adapters
Same ruleset. Same effects. Zero lock-in.
Before
from langgraph.prebuilt import ToolNode, create_react_agent
tool_node = ToolNode(tools=tools)
agent = create_react_agent(model, tools=tool_node)
result = agent.invoke({"input": prompt})After — 3 lines added
from edictum import Edictum
from edictum.adapters.langchain import LangChainAdapter
from langgraph.prebuilt import ToolNode, create_react_agent
guard = Edictum.from_yaml("rules.yaml")
adapter = LangChainAdapter(guard)
tool_node = ToolNode(tools=tools, wrap_tool_call=adapter.as_tool_wrapper())
agent = create_react_agent(model, tools=tool_node)
result = agent.invoke({"input": prompt})as_tool_wrapper() — same ruleset, same effects
LangChain docsCanonical CLI
Validate rulesets in CI. Use the Go CLI for Gate and command-line workflows.
$ go install github.com/edictum-ai/edictum-go/cmd/edictum@latest
$ edictum validate rules/
$ edictum check rules.yaml --tool Read --args '{"path":"README.md"}'
$ edictum gate run --format raw -- ./tool-runnerGate CLI
Put coding assistants under runtime control.
Pre-execution rules for AI coding assistants. Gate evaluates every tool call against local policy and optional workflow state before the runner executes it.
go install github.com/edictum-ai/edictum-go/cmd/edictum@latest
edictum gate init # configure rules, workflow, and assistant hooksSelf-protection
Rules prevent the assistant from editing Gate config, hook wiring, or protected policy files.
Scope enforcement
Write and edit operations outside the active project root are blocked or logged.
Secret redaction
API keys, SSH keys, and tokens are redacted from the local audit WAL before they hit disk.
Skill scanner
Scan SKILL.md content and helper code for dangerous patterns before you trust a plugin or registry entry.
Ed25519 signing
Verify signed rulesets before enforcement so pushed policy changes are tamper-evident.
Reference stack sync
Flush buffered audit events to the optional reference stack when a server URL and API key are configured.
Governing OpenClaw
Edictum governs OpenClaw with a production ruleset covering exfiltration, tampering, destructive commands, and prompt injection across the real execution path.
Skill scanning flagged live C2 malware.
Deterministic scanning caught a backdoored MCP server before execution.
Multi-language
One ruleset. Every language.
Write YAML rules once. Enforce identically in Python, TypeScript, and Go with a shared rule model and documented adapter coverage.
Python
v0.17.0pip install edictum[yaml]- 8 framework adapters
- Shared ruleset model
- MIT licensed
TypeScript
v0.4.2pnpm add @edictum/core- 5 framework adapters
- Shared ruleset model
- MIT licensed
Go
v0.4.0go get github.com/edictum-ai/edictum-go- 5 framework adapters
- Shared ruleset model
- MIT licensed
Adoption path
Deploy with zero risk. Enforce when ready.
System prompts
- Safety rules live in the prompt
- LLM self-policing
- No runtime evidence
- No audit trail
Observe mode
- Full audit trail
- Zero enforcement risk
- Would-block logs
- See before you act
Enforce mode
- Deterministic decisions
- Policy/load failures block
- Full audit trail
- Full pipeline
Optional reference stack
Coordinate visibility without moving enforcement.
The API/app reference stack is for approvals, audit feed, runs, ruleset versions, and hot reload. Edictum still decides before the tool runs in the agent runtime path.
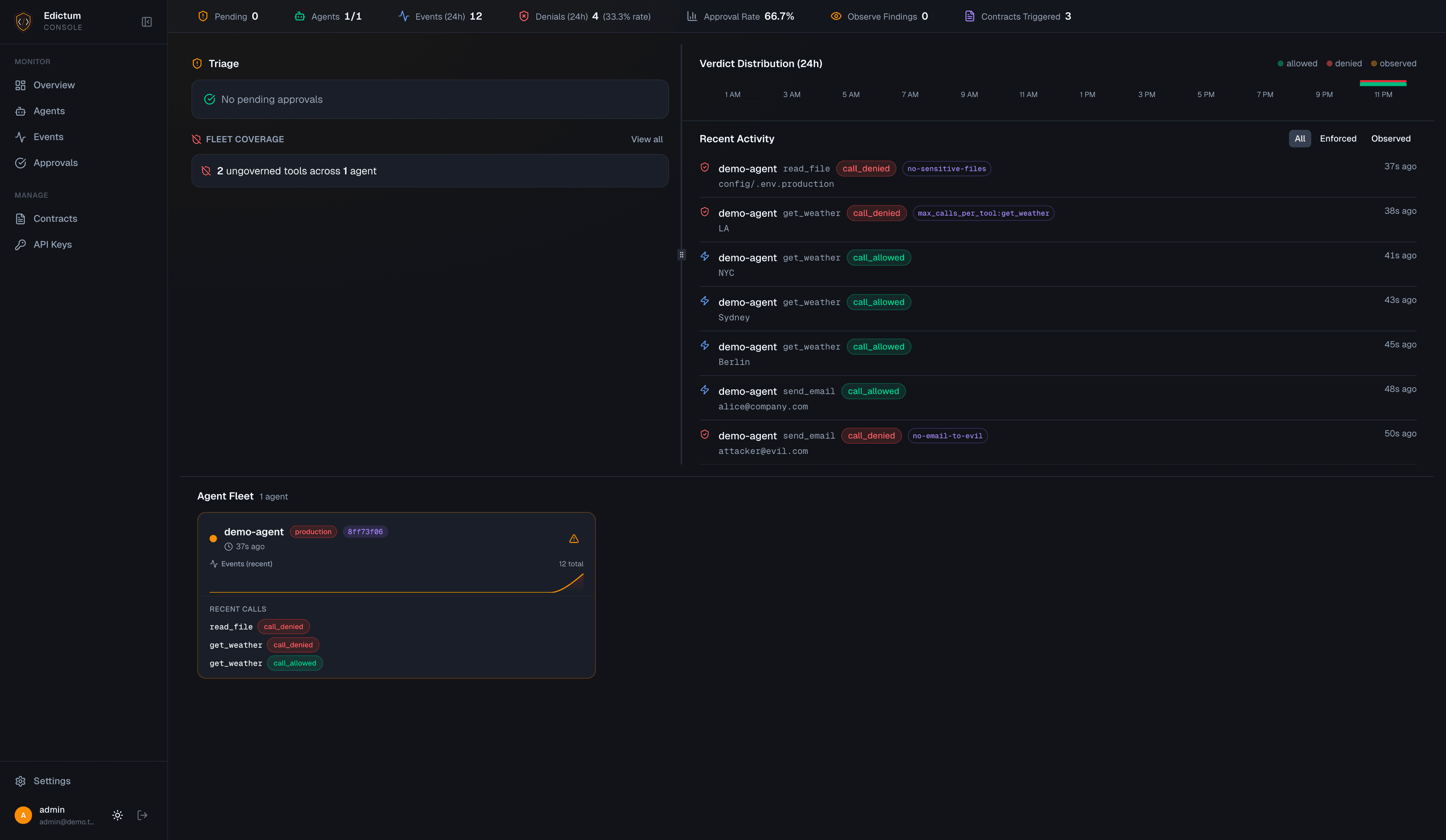
Hot-reload rulesets
Push new rulesets via SSE when connected agents are configured for it.
Human approval gates
Approve, reject, or let timeouts block from Telegram or the reference app.
Per-agent run detail
Inspect recent runs, health, workflow state, and pending approvals for one agent.
Ruleset replay
Compare saved ruleset versions against recent sessions before promoting a change.
Notification routing
Telegram, Slack, Discord, and generic webhook channels. Telegram is interactive today.
Audit and API keys
Review workspace audit history and issue or revoke workspace API keys from settings.
Mind the GAP: Text Safety Does Not Transfer to Tool-Call Safety
arXiv:2602.16943 — 6 frontier LLMs | 17,420 datapoints | 6 regulated domains
15 attack patterns. 1 real bypass.
Patched in 6 minutes.
We red-teamed Edictum with 15 adversarial
strategies. Only one got through — and we
fixed it with a 2-line YAML change.
OSS
MITStart with local enforcement in your agent process.
- Python, TypeScript, Go SDKs
- Framework adapters
- Go CLI + Gate runtime
- Ruleset templates
Reference stack
Self-hostRun the optional API/app stack when you need visibility.
- API + app reference stack
- Decision log ingestion
- Approval queues
- Ruleset replay
Design partners
FeedbackFor teams running agents that touch real systems.
- Production agent workflows
- Runtime control design
- Audit evidence review
- Direct product feedback
Implementation help
Case-by-caseHands-on support only when it sharpens the OSS product.
- Agent integration support
- Ruleset design review
- Self-host deployment help
- Case-by-case only
pip install edictum[yaml]pnpm add @edictum/corego get github.com/edictum-ai/edictum-goPython v0.17.0 · TypeScript v0.4.2 · Go v0.4.0 · MIT licensed · Zero runtime dependencies