AI models say “no” in text. Then do it with tool calls.
The safety gap
your guardrails miss.
GPT-5.2: 21.3% GAP rate. Claude: 1.7%. Every model has the gap.
Deterministic contracts that execute outside the model. Can't be prompt-injected. Fail-closed by default.
pip install edictumGet started
Three lines. Full enforcement.
pip install edictum
guard = Edictum.from_template("file-agent")
# Done. Agents can't delete files or read .env.file-agent
Block sensitive file reads and destructive bash commands
3 contractsresearch-agent
Session limits and PII detection for research workflows
3 contractsdevops-agent
Production deploy gates, ticket requirements, role checks
6 contractsnanobot-agent
HITL approvals for shell exec, sub-agent spawning, MCP tools
5 contractsFramework adapters
Same contract. Same effects. Zero lock-in.
Before
from langgraph.prebuilt import ToolNode, create_react_agent
tool_node = ToolNode(tools=tools)
agent = create_react_agent(model, tools=tool_node)
result = agent.invoke({"input": prompt})After — 3 lines added
from edictum import Edictum
from edictum.adapters.langchain import LangChainAdapter
from langgraph.prebuilt import ToolNode, create_react_agent
guard = Edictum.from_yaml("contracts.yaml")
adapter = LangChainAdapter(guard)
tool_node = ToolNode(tools=tools, wrap_tool_call=adapter.as_tool_wrapper())
agent = create_react_agent(model, tools=tool_node)
result = agent.invoke({"input": prompt})as_tool_wrapper() — same contract, same effects
LangChain docsCLI tools
Validate contracts in CI. Test before deploy.
$ edictum validate contracts/
$ edictum check --tool read_file --args '{"path": ".env"}'
$ edictum test --cases tests.yamlEdictum Gate
New in v0.15.0Govern your coding assistant.
Pre-execution governance for AI coding assistants. Gate sits between the assistant and your OS, evaluating every tool call against YAML contracts before it runs.
pip install edictum[gate]
edictum gate init # wizard deploys contracts + registers hooksSelf-protection
Always-enforced contracts prevent the assistant from reading, writing, or disabling Gate config.
Scope enforcement
Write/Edit operations outside the project directory are denied or logged.
Secret redaction
API keys, SSH keys, and tokens are redacted from the audit WAL before they hit disk.
Console sync
Auto-flush to Edictum Console every 30s. Manual flush with edictum gate sync.
Adoption path
Deploy with zero risk. Enforce when ready.
System prompts
- Safety rules live in the prompt
- LLM self-policing
- No visibility
- No audit trail
Observe mode
- Full audit trail
- Zero enforcement risk
- CALL_WOULD_DENY logs
- See before you act
Enforce mode
- Deterministic verdicts
- Fail-closed by default
- Full audit trail
- Full pipeline
Session limits
Cap total calls, per-tool calls, and attempts per session.
Sandbox enforcement
Restrict file access to allowed paths. Deny outside.
Principal identity
Role-based rules. Different principals, different permissions.
Pipeline architecture
Pre, post, session, sandbox — evaluated in order.
Operations console
See everything. Control everything.
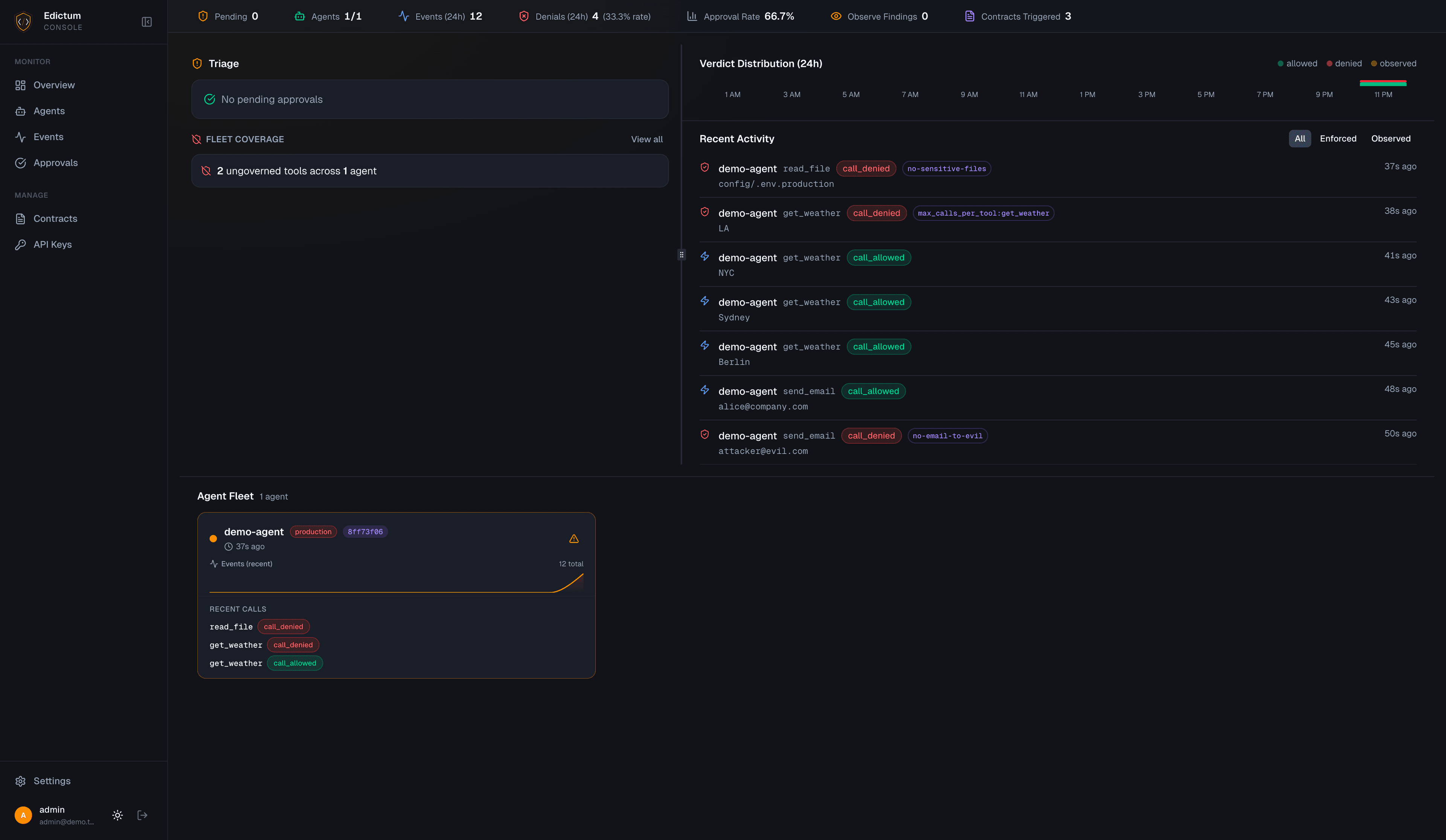
Hot-reload contracts
Push new contract bundles via SSE. No agent restarts.
Human-in-the-loop approvals
Approve or deny from Slack, Telegram, or Discord.
Fleet drift detection
Coverage analysis across your entire agent fleet.
AI contract assistant
Generate contracts from natural language. Anthropic, OpenAI, or Ollama.
Notification routing
Slack, Telegram, Discord, Email, MS Teams, Webhook. Splunk coming soon.
Assignment rules
Route agents to contract bundles by pattern, tag, or environment.
Mind the GAP: Text Safety Does Not Transfer to Tool-Call Safety
arXiv:2602.16943 — 6 frontier LLMs | 17,420 datapoints | 6 regulated domains
15 attack patterns. 1 real bypass.
Patched in 6 minutes.
We red-teamed Edictum with 15 adversarial
strategies. Only one got through — and we
fixed it with a 2-line YAML change.
Console
FSL-1.0-Apache-2.0Free
- Self-hosted
- Fleet monitoring
- Human-in-the-loop approvals
- Audit feed